| Lesson 5 | Subnets |
| Objective | Explain the purpose of subnetting and subnet masks |
Purpose of Subnet Masks
What is Subnetting?
There is a scarcity of network addresses today. A viable solution to creating new network addresses is to divide the 32-bit address in a process called subnetting. The process entails modifying the IP address by using the host (or client portion) address bits as network address bits. A more technical evaluation is that a subnet mask is applied to filter the bits not used in the network address. A subnet mask is a 32-bit number, written in dotted decimal form, in much the same way an IP address is displayed.
For example
255.255.255.192only hosts IP addresses that are on the same subnet and can communicate with others without a router.
Subnetting is used when a company has more computers than can be connected to its network; it is also used as a traffic reduction mechanism. However, all devices on the subnet must be programmed with the correct mask value in order for the network to function properly.
Since subnetting tricks the IP Address by turning an unused portion of the 1)public address into a 2)private address
(as discussed at the end of Lesson 4). Subnetting can only occur within a LAN setting, and requires a great deal of caution.
An incorrect subnetting scheme may violate IP addressing standards, which could cause the network address to be misinterpreted by Internet protocols. This would result in widespread communications problems.
IP Addresses
You know that DNS translates domain names into IP addresses. You also know that IP addresses and domain names are registered and allocated by ICANN. This page provides more information about the IP addressing system used with IPv4. An IPv4 address is 32 bits long and every node on the Internet has a unique address. The 32 bits are divided into four octets for easier reading. In the earlier days of the Internet, these octets also identified the assignee to some extent, however that is less true today. Nevertheless, IP addresses are still assigned in blocks. The addresses in a block are contiguous, and the number of addresses in a block must be a power of two. A block is assigned by specifying a given number of bits, from left to right where the remaining bits represent addresses in the block.
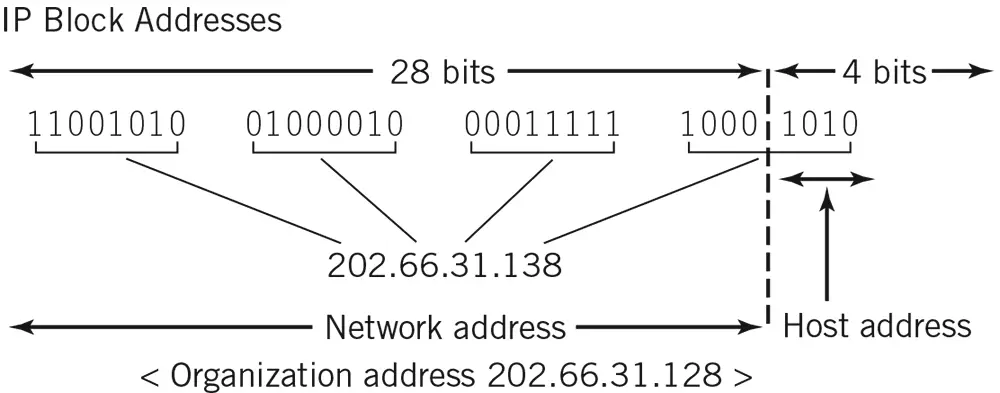
First Address in block is Network Address
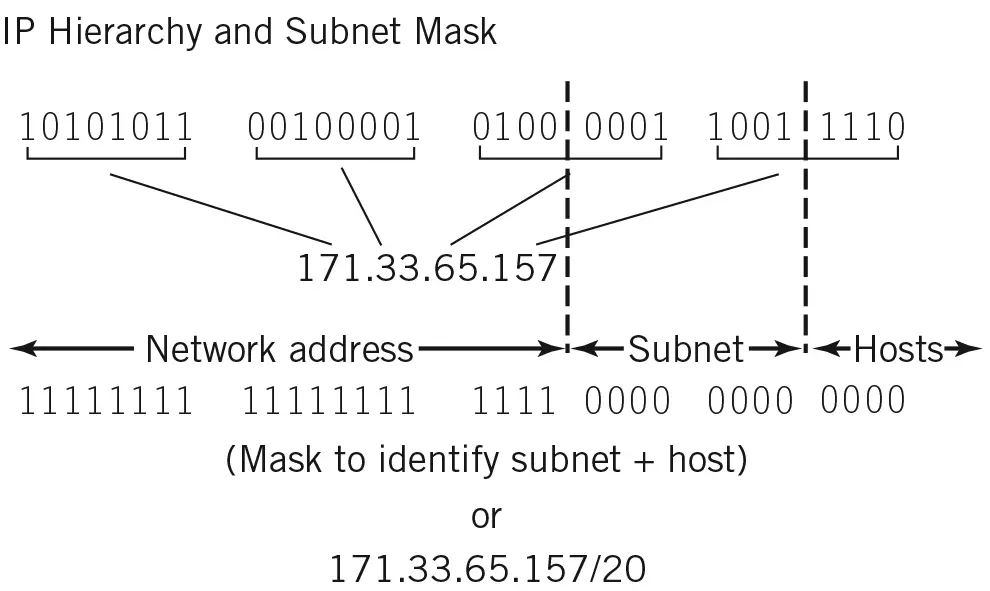
Look at Figure 4-5. For example, if your organization is issued a block starting with the 28 bits to the left of the dividing line in the figure, the four remaining bits would provide a block of sixteen addresses for computers within your organization. Your organization could allocate these sixteen addresses any way it wishes. The first address in the block is defined as the network address for your organization; it is used for routing. Traditionally, most blocks are larger than sixteen addresses, and IP addresses are usually divided into three levels, and in some cases four or more. Figure 4.5.1 shows an IP address divided into three levels where the top level is the network address. The remaining bits are divided into subnets where each subnet has a number of hosts (or nodes). Masks are used to separate the different parts of the address. A mask consists of a number of 1s followed by 0s. When the mask is suitably combined with the IP address using Boolean algebra, individual components of the address can be identified. A mask is specified by placing a slash mark with the number of 1s at the end of the IP address. Alternatively, it can be specified in dotted decimal notation. Both notations are shown in the figure.
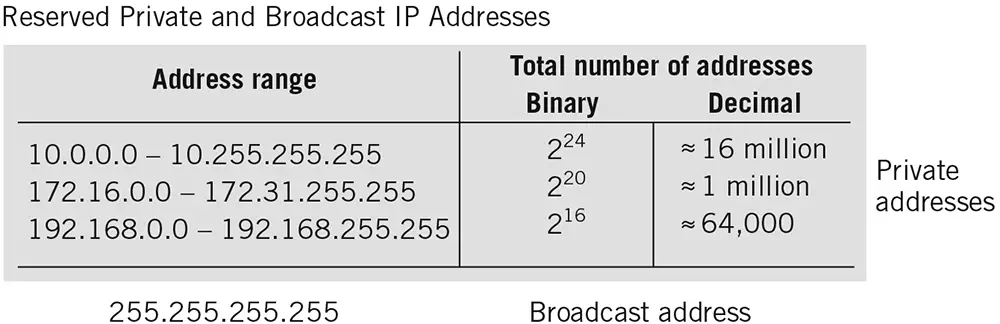
A number of IP addresses are reserved for private use. These IP addresses may not be used on the Internet, but they are suitable for networks which are not directly exposed to the Internet. There is also a universal broadcast address consisting of all 1s that addresses all nodes on a subnet. The private addresses are listed in Figure 4.5.2
A number of IP addresses are reserved for private use. These IP addresses may not be used on the Internet, but they are suitable for networks which are not directly exposed to the Internet. There is also a universal broadcast address consisting of all 1s that addresses all nodes on a subnet. The private addresses are listed in Figure 4.5.2
Reserved Private Broadcast Ip Addresses
Amazon VPC Subnet
A subnet is a segment of an Amazon VPC’s IP address range where you can launch
- Amazon EC2 instances,
- Amazon Relational Database Service (Amazon RDS) databases, and
- other AWS resources.
Vulnerabilities of Address Resolution Protocol
Subnet Masks
To subnet an IP network, you use a subnet mask, which splits IP networks into subgroups of networks or subnetworks by filtering unwanted bits so that only usable bits remain. Before using subnet masks, you must perform a decimal-to-binary conversion of the IP address. A subnet mask identifies how the bits of an IP address are used. In binary terms, 0 and 1 are the only functional digits. In binary notation, a 0 (zero) indicates that the bit is a host bit. A 1 (one) indicates that the bit is a network bit.
A subnet mask defines the network, the subnet, and the host.
The table below provides the default masks for IP address classes A to C.
A subnet mask defines the network, the subnet, and the host.
The table below provides the default masks for IP address classes A to C.
| Class | Default mask |
|---|---|
| A | 255.0.0.0 |
| B | 255.255.0.0 |
| C | 255.255.255.0 |
In the next lesson, you will learn about remote access protocols.
Client Server Architecture